Stay ahead. Stay secure.
Take control of cyber risk with the only platform that spans your supply chain, attack surface, workforce, and trust relationships.
Our Services
End-to-End Security Services
From offensive testing to strategic advisory - we cover every layer of your security lifecycle.
Platform
One Platform. Complete Visibility.
Explore every dimension of your security posture from a single pane of glass.
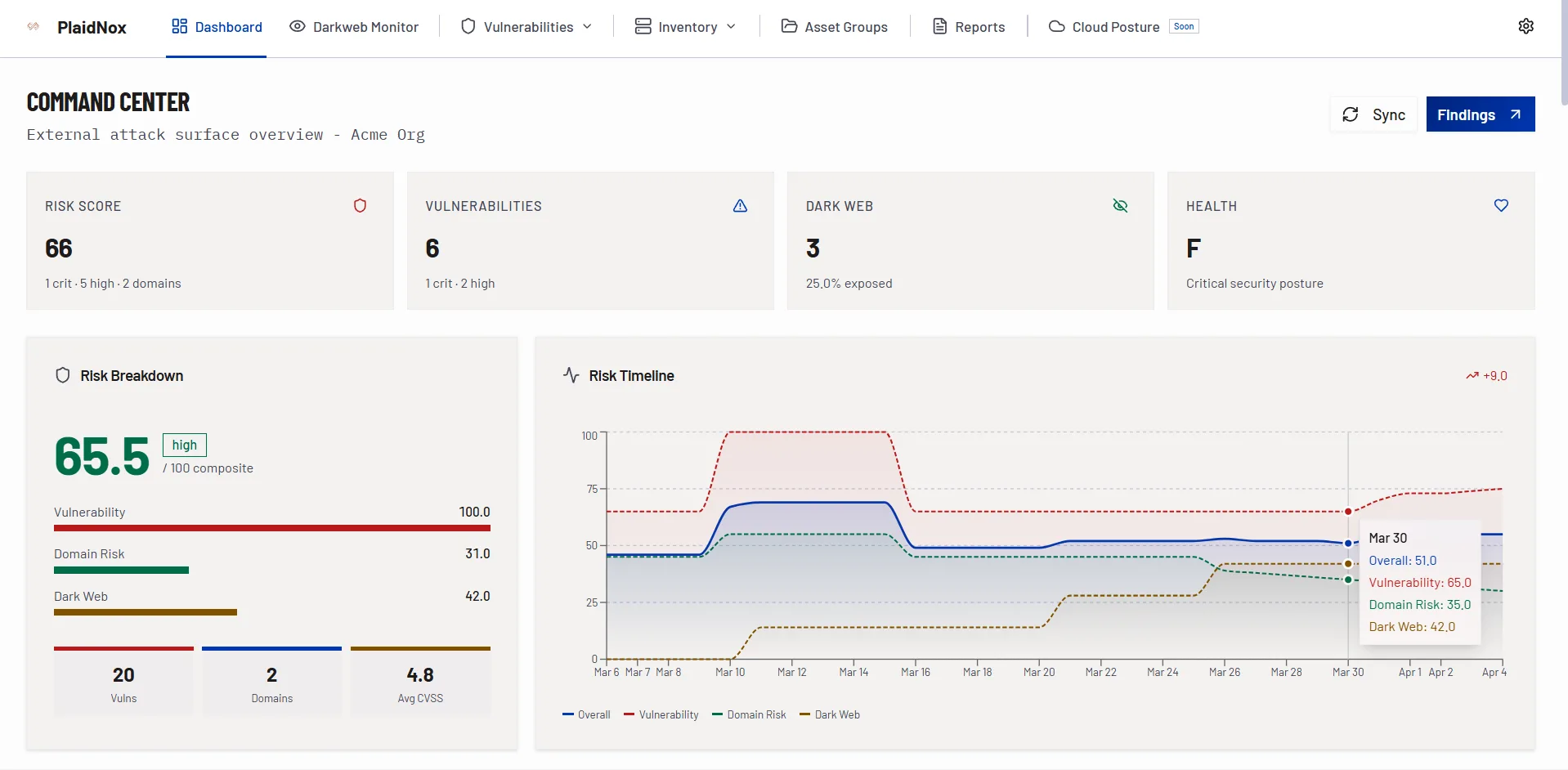
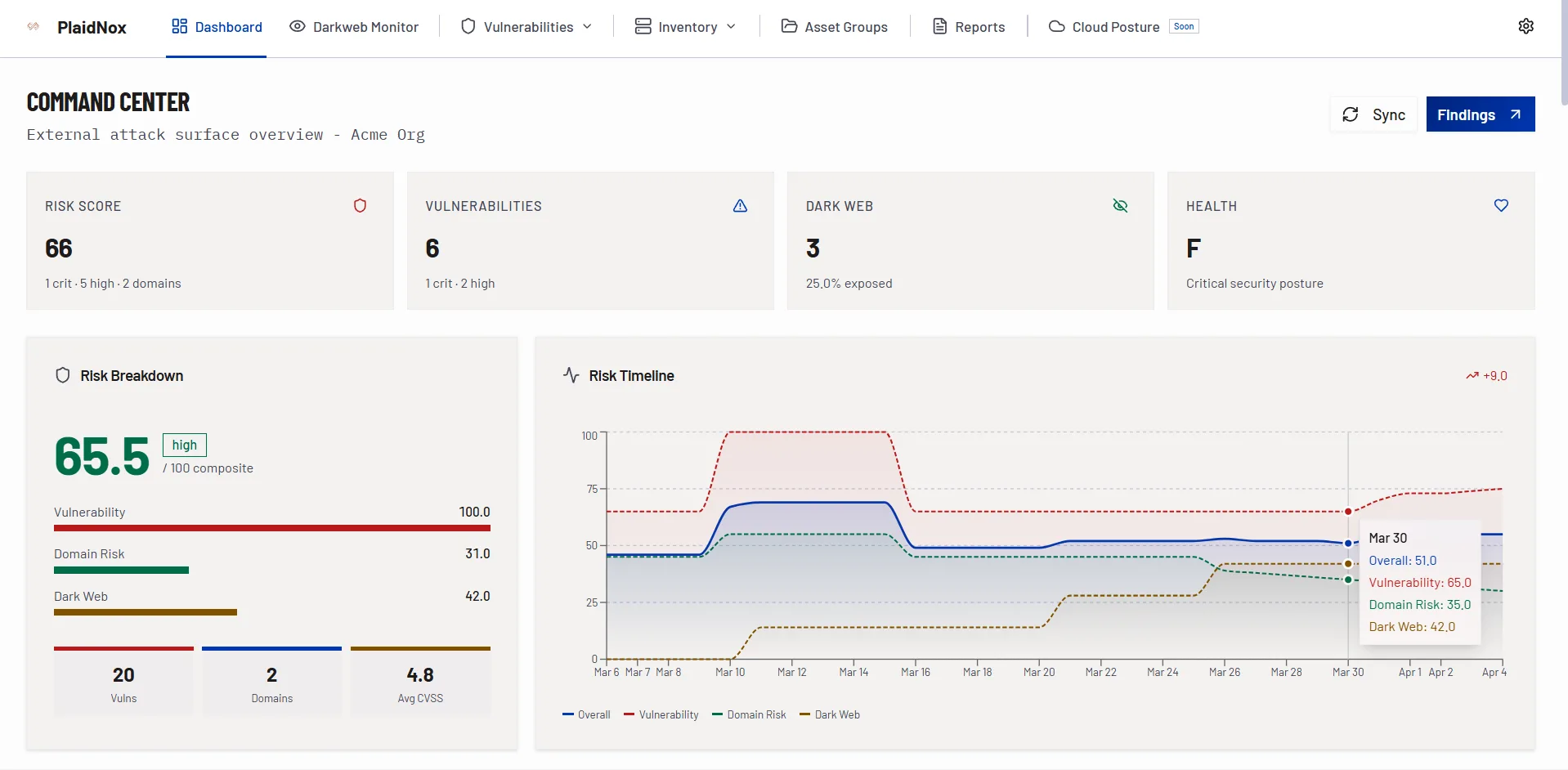
Executive overview with risk scores, vulnerability counts, and asset discovery stats.
Security Posture
Security-First. Zero Trust. Everywhere.
Improve your security posture externally and internally. Build Zero Trust from the ground up.
Use Cases
How PlaidNox Transforms Security
Configuration & Advisory
We Help Organizations Build & Configure Security Infrastructure
From initial architecture to ongoing optimization - PlaidNox provides hands-on expertise to configure, harden, and maintain your security stack. We help organizations place security first, build Zero Trust, and improve security posture externally and internally.
PAM Implementation
Deploy and configure CyberArk, BeyondTrust, or Delinea. Vault credentials, enforce session recording, implement just-in-time access, and establish privileged account lifecycle governance.
SIEM Deployment & Tuning
Set up Splunk, Sentinel, QRadar, or Elastic SIEM. Create custom detection rules, reduce alert fatigue by 70%+, build correlation logic, and integrate threat intelligence feeds.
SOC Build & Optimization
Design SOC workflows, create incident response playbooks, implement SOAR automation, define escalation matrices, and establish 24/7 monitoring procedures.
Identity & Access Management
Configure Okta, Azure AD, Ping Identity, or ForgeRock. Implement SSO, MFA, conditional access policies, identity lifecycle automation, and access certification campaigns.
Firewall & Network Security
Optimize Palo Alto, Fortinet, or Check Point rules. Implement micro-segmentation, ZTNA policies, network access control, and IDS/IPS tuning.
Use-Case Development
Create custom detection use-cases, threat hunting queries, automated response workflows, and compliance monitoring dashboards tailored to your industry and threat landscape.
Platform Highlights
Built for Security Teams, Loved by CISOs
Every view is designed to surface what matters - from real-time notifications to detailed vulnerability analysis.
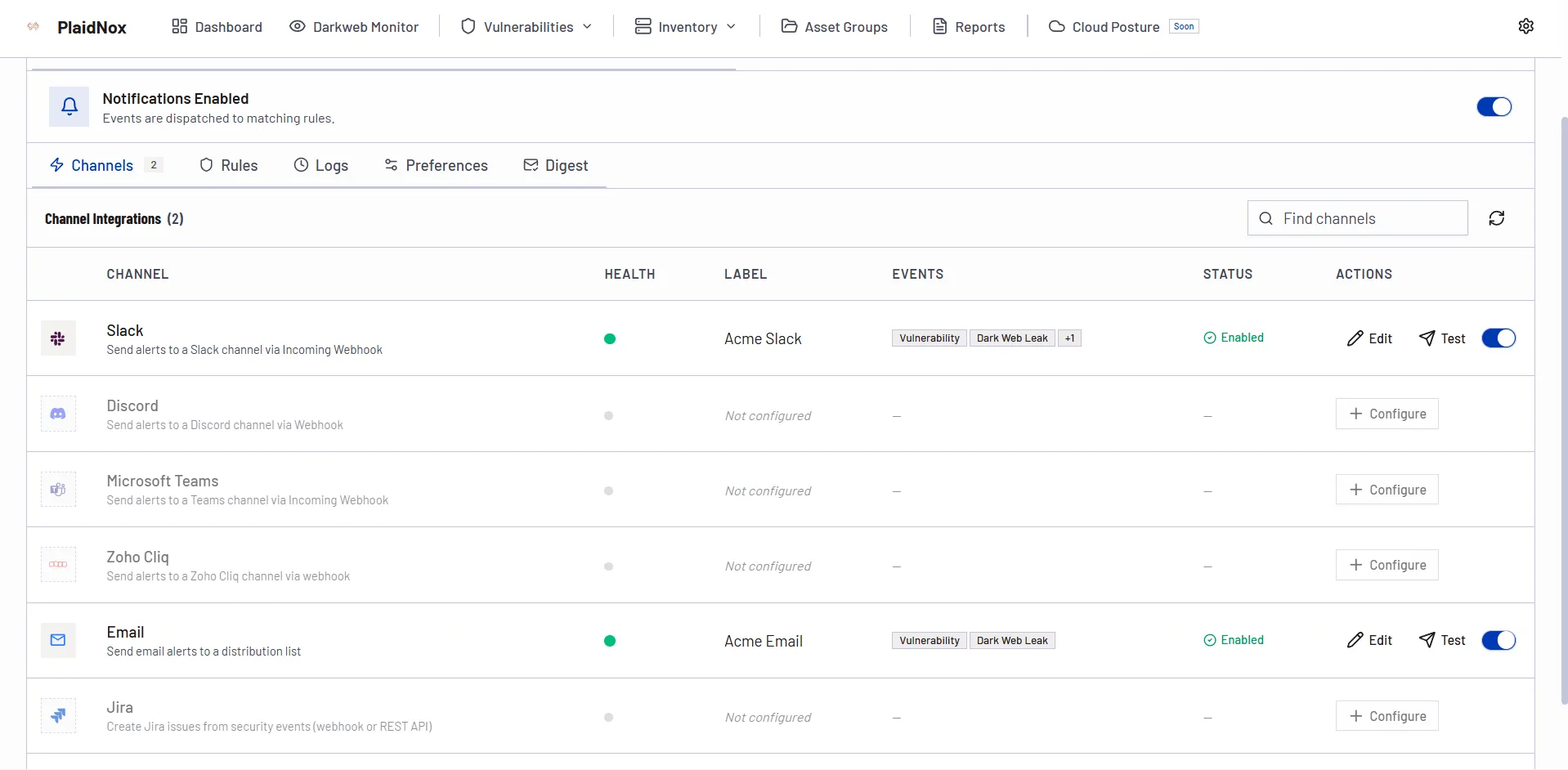
Real-Time Notifications
Stay on top of critical findings, remediation deadlines, and team activity with intelligent notification feeds.
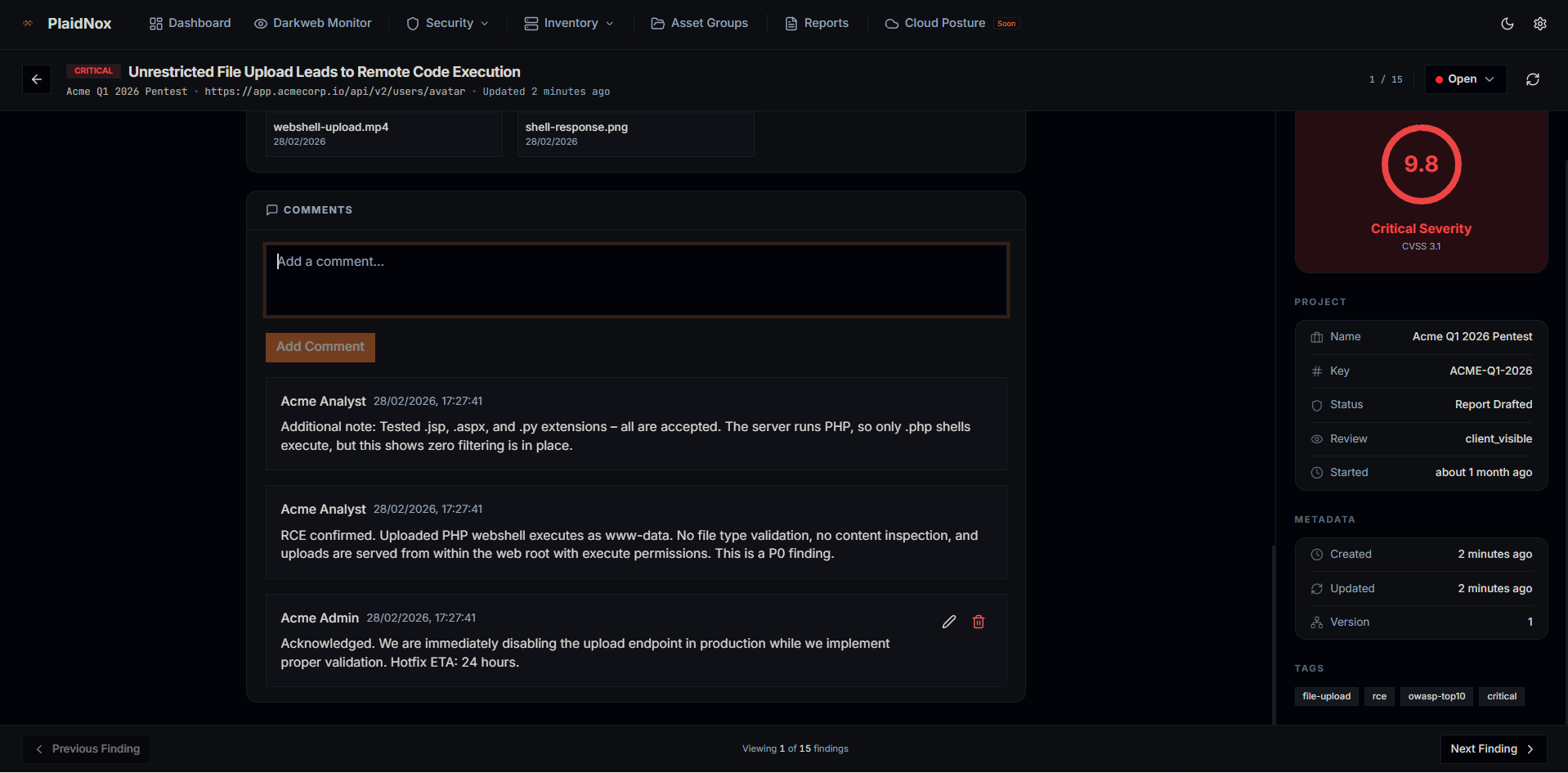
Collaborative Workflow
Comment on findings, assign tasks, and coordinate remediation directly within the platform.
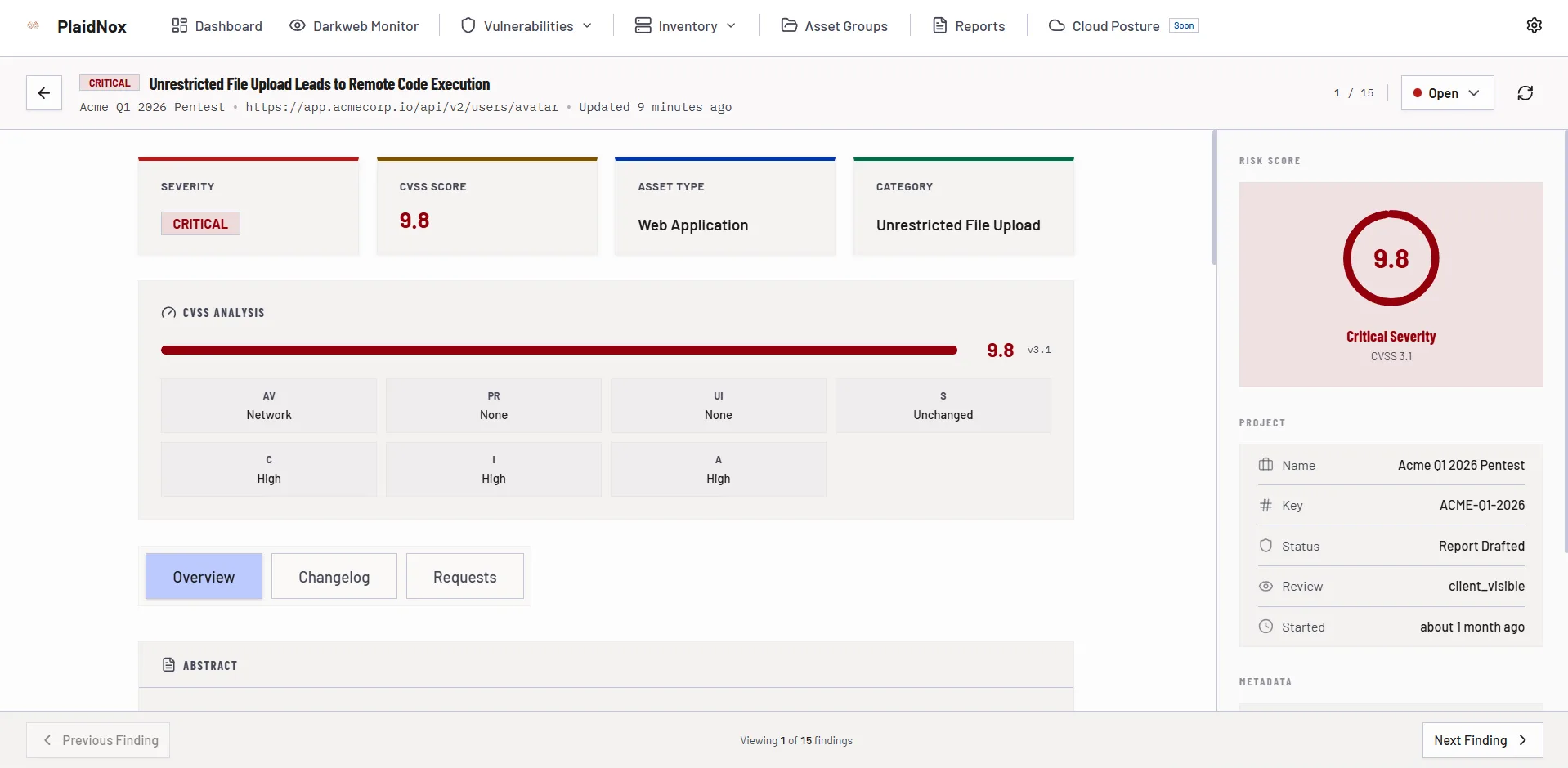
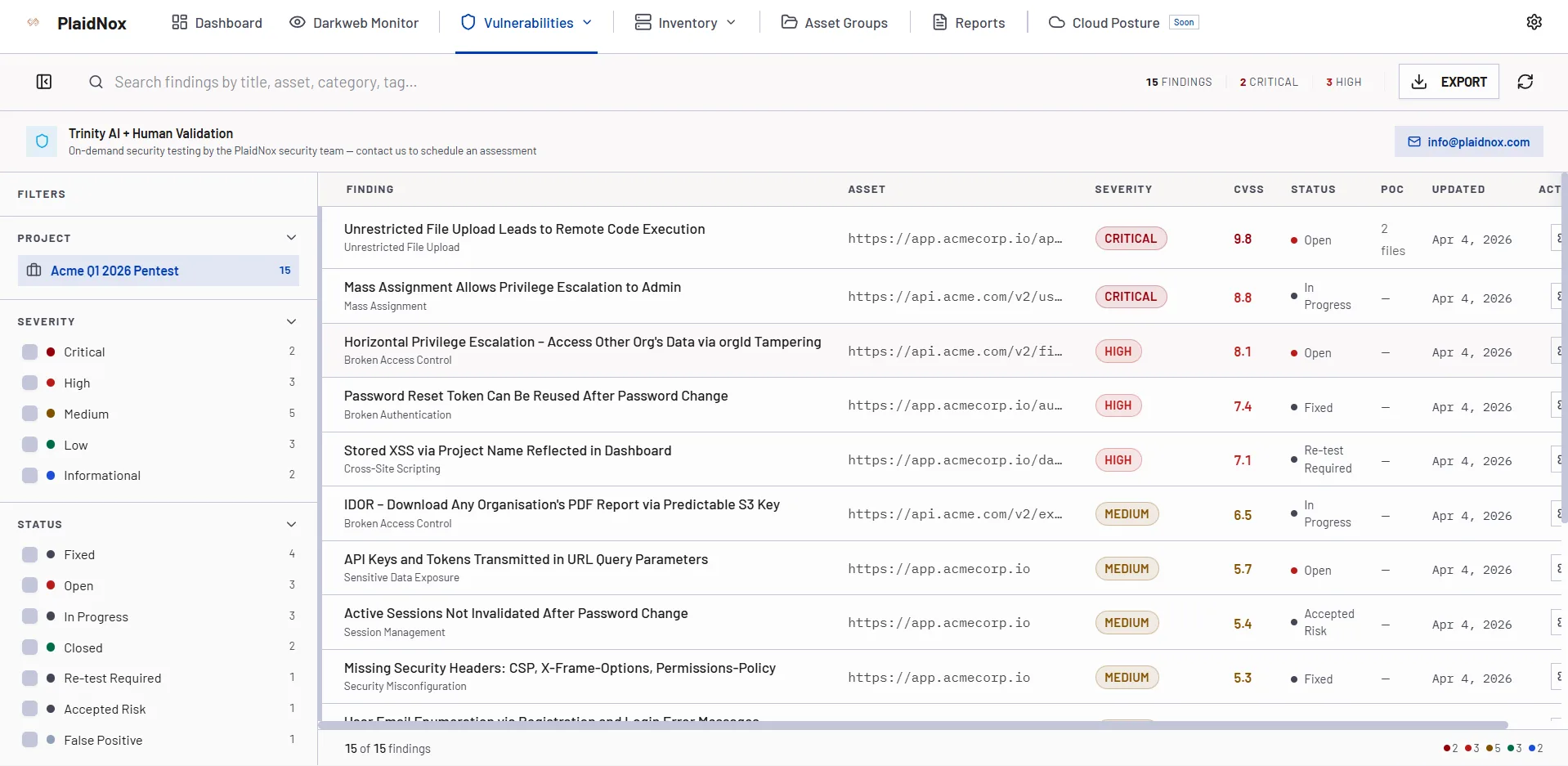
Vulnerability Deep-Dive
Detailed vulnerability analysis with CVSS scoring, exploit availability, and step-by-step remediation guidance.
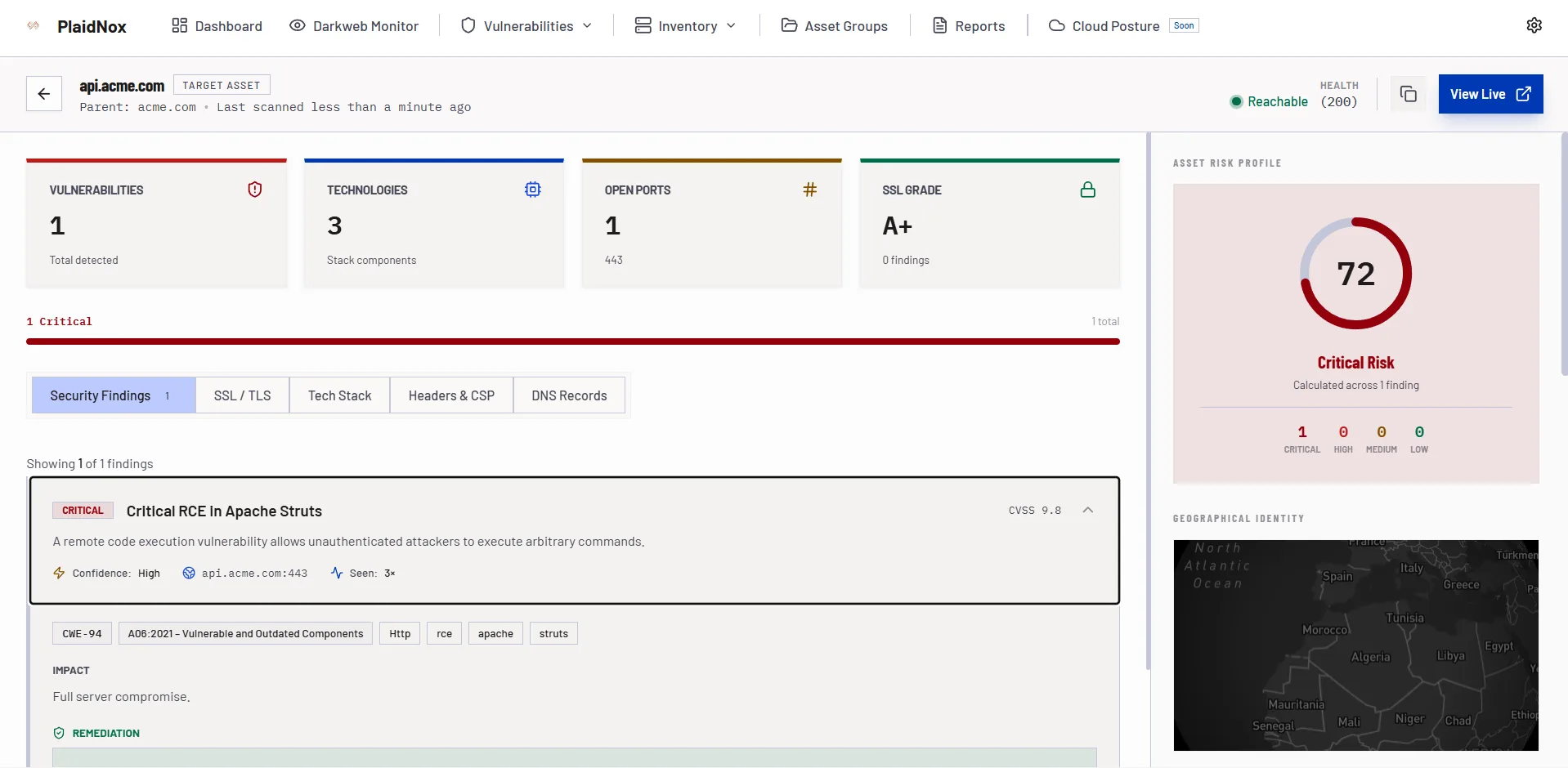
Investigation & Triage
Correlated attack paths, evidence collection, and guided investigation workflows for faster response.