Dark Web
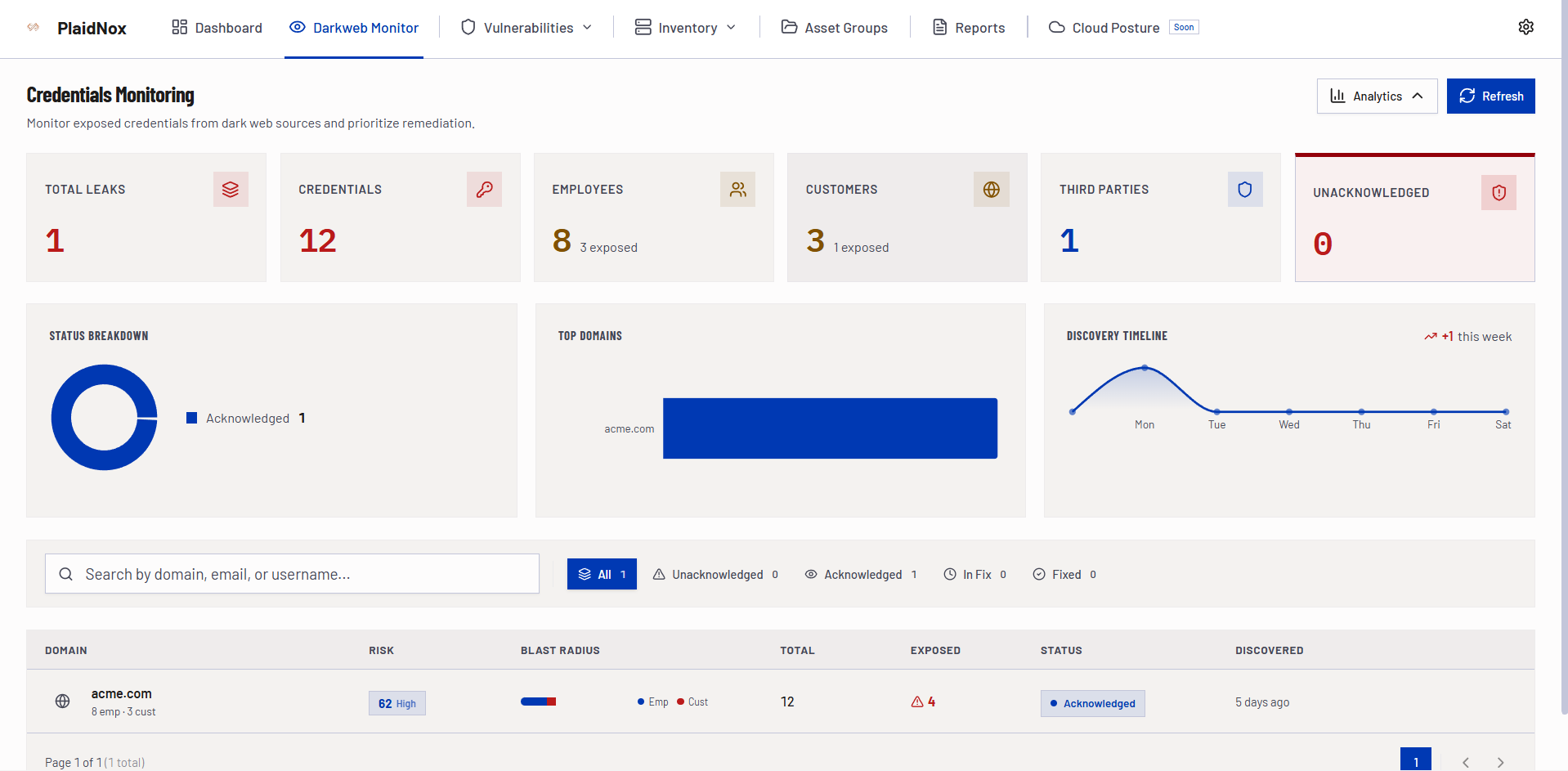
Credential Monitoring
Know the moment your credentials are exposed. Veta Credential Monitor continuously scans dark web forums, stealer logs, and underground channels - delivering enriched, validated findings with blast-radius scoring and response playbooks.
Real-Time, Not Batch
Unlike legacy dark web services that deliver weekly batch reports, Veta Credential Monitor alerts you the moment new credentials surface - validated by human analysts within hours, not days.
Blast Radius Precision
- Scores every leak by blast radius - systems, services, and accounts affected
- Segments credentials by employee vs. customer vs. third-party
- Human analysts validate before escalation - no raw dump noise
- Enriches findings with source, timestamp, and threat actor profile
- Delivers response playbooks alongside every critical alert
Detection Capabilities
From Detection to Response. One Continuous Workflow.
Credential leaks, brand mentions, code exposure - enriched, validated, and routed to your team in real time.
Credential Leak Detection
Continuous scanning of stealer logs, combolists, and dark web dumps for email/password pairs linked to your domains. Every leak scored by blast radius and freshness.
- Email and password pair detection across stealer logs and combolists
- Blast-radius scoring - quantifying affected systems and accounts
- Credential age and freshness analysis for prioritization
- Password pattern analysis to identify reuse and weak policies
Foundation of every Veta Credential Monitor engagement.
Dark Web & Underground Monitoring
Crawlers and analysts inside invite-only forums, Telegram groups, and underground marketplaces - capturing brand mentions, data listings, and threat actor activity.
- Closed marketplace and broker chat surveillance
- Telegram and Discord extortion room monitoring
- Threat actor tracking with alias and wallet correlation
- Brand impersonation and phishing domain detection
We operate where attackers trade - so you don't have to.
Response Playbooks & Remediation
Detection without response is just awareness. Pre-built playbooks trigger identity resets, coordinate takedowns, and build threat actor dossiers automatically.
- Credential reset and MFA enforcement workflows
- Legal and takedown coordination for high-risk listings
- Threat actor profiling with campaign history
- Remediation lifecycle tracking (Open → In Progress → Resolved)
From detection to remediation - one continuous workflow.
What We Monitor
Broad Source Coverage for Complete Visibility
Our collection mesh covers every corner of the underground - not just the surface-level dark web.
Stealer Logs & Malware Panels
- Freshly harvested credentials from infostealer malware
- Session tokens, cookies, and browser-saved passwords
- Automated correlation with your domain footprint
Forums & Marketplaces
- Invite-only dark web forums and broker channels
- Data listing and auction monitoring
- Threat actor activity and reputation tracking
Code Repositories & Paste Sites
- Leaked source code, API keys, and internal docs
- Public and private repo scanning for secrets
- Paste site and code-sharing platform monitoring
Messaging & Social Channels
- Telegram groups and Discord extortion rooms
- Ransom negotiation and data leak announcement channels
- Brand impersonation across phishing infrastructure
How Veta Credential Monitor Works
Five Continuous Phases with Human Validation
From dark web collection to credential reset - every step is enriched, validated, and actionable.
Collection Mesh
Crawlers and human analysts continuously harvest data from 6+ source categories across the dark web.
Enrichment Engine
Every finding is enriched with blast-radius scoring, employee/customer segmentation, and source context.
Analyst Validation
Human analysts confirm legitimacy, translate foreign-language posts, and correlate actor behavior.
Intelligent Routing
Validated findings route to Slack, Teams, SIEM, or email with severity-based escalation rules.
Response Automation
Pre-built playbooks trigger credential resets, legal takedowns, and threat actor dossier updates.
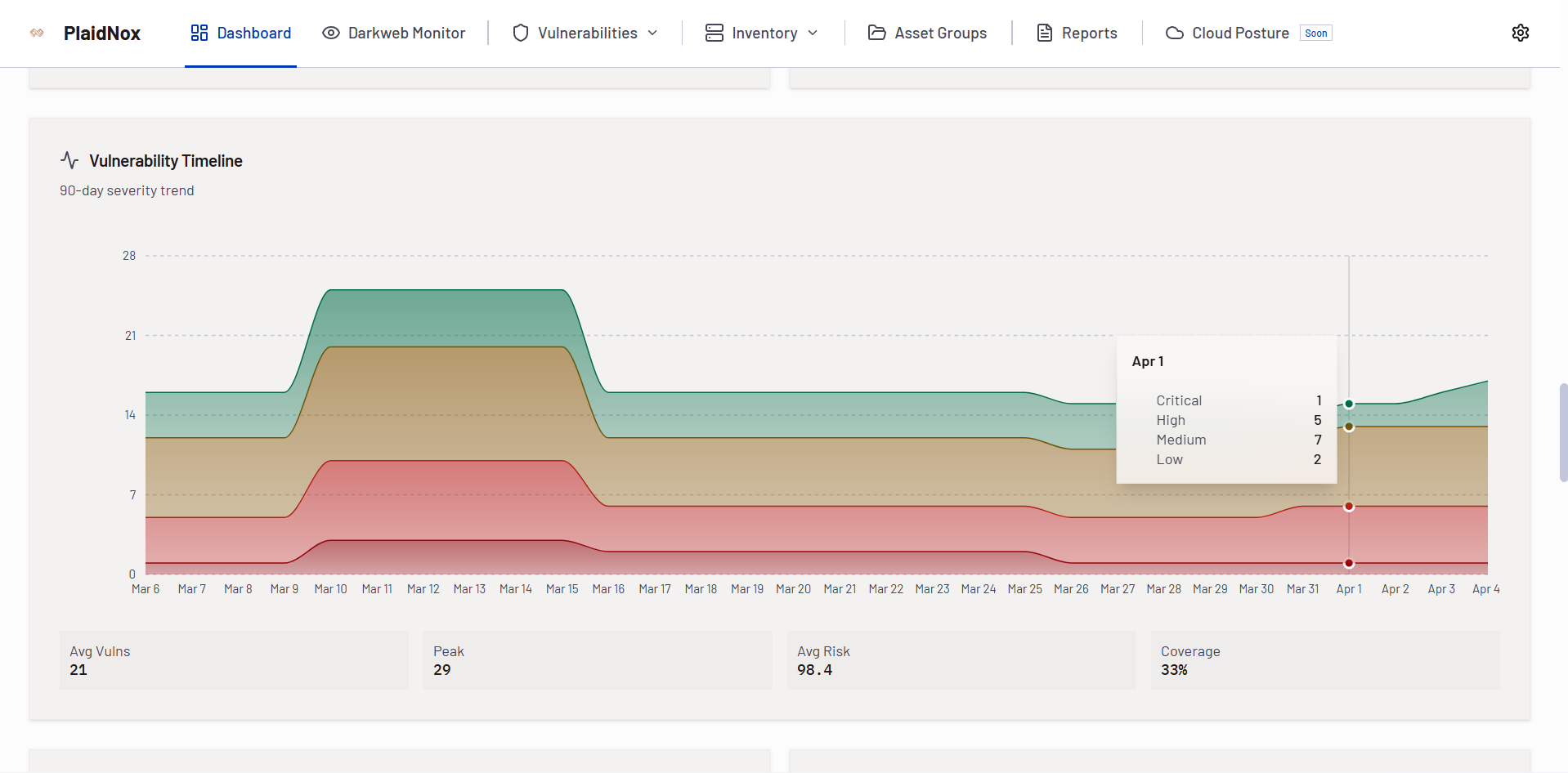
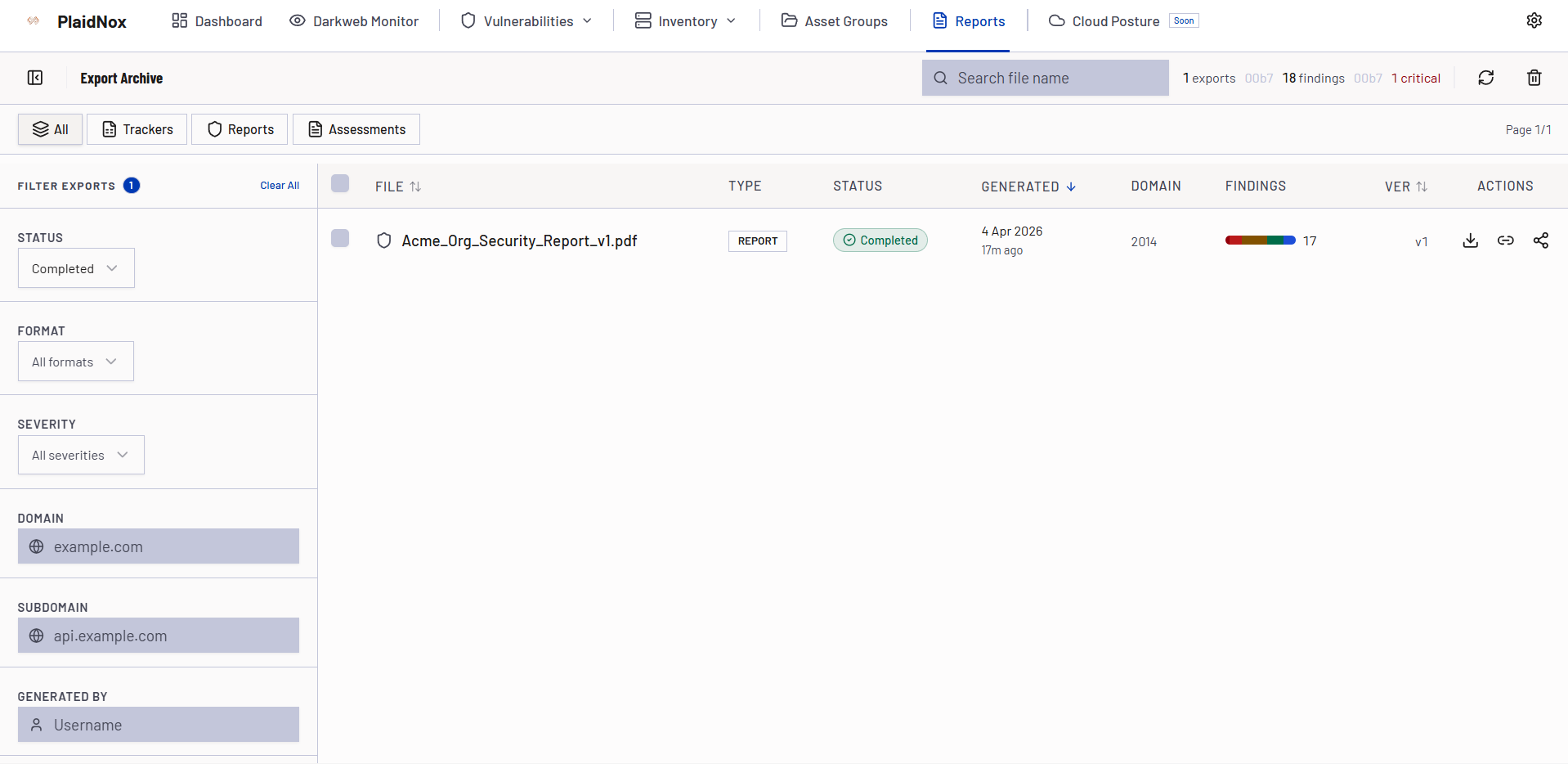
Veta Platform
See Veta Credential Monitor in Action
Explore the platform - from real-time exposure dashboards to multi-channel alerting and actionable reports.
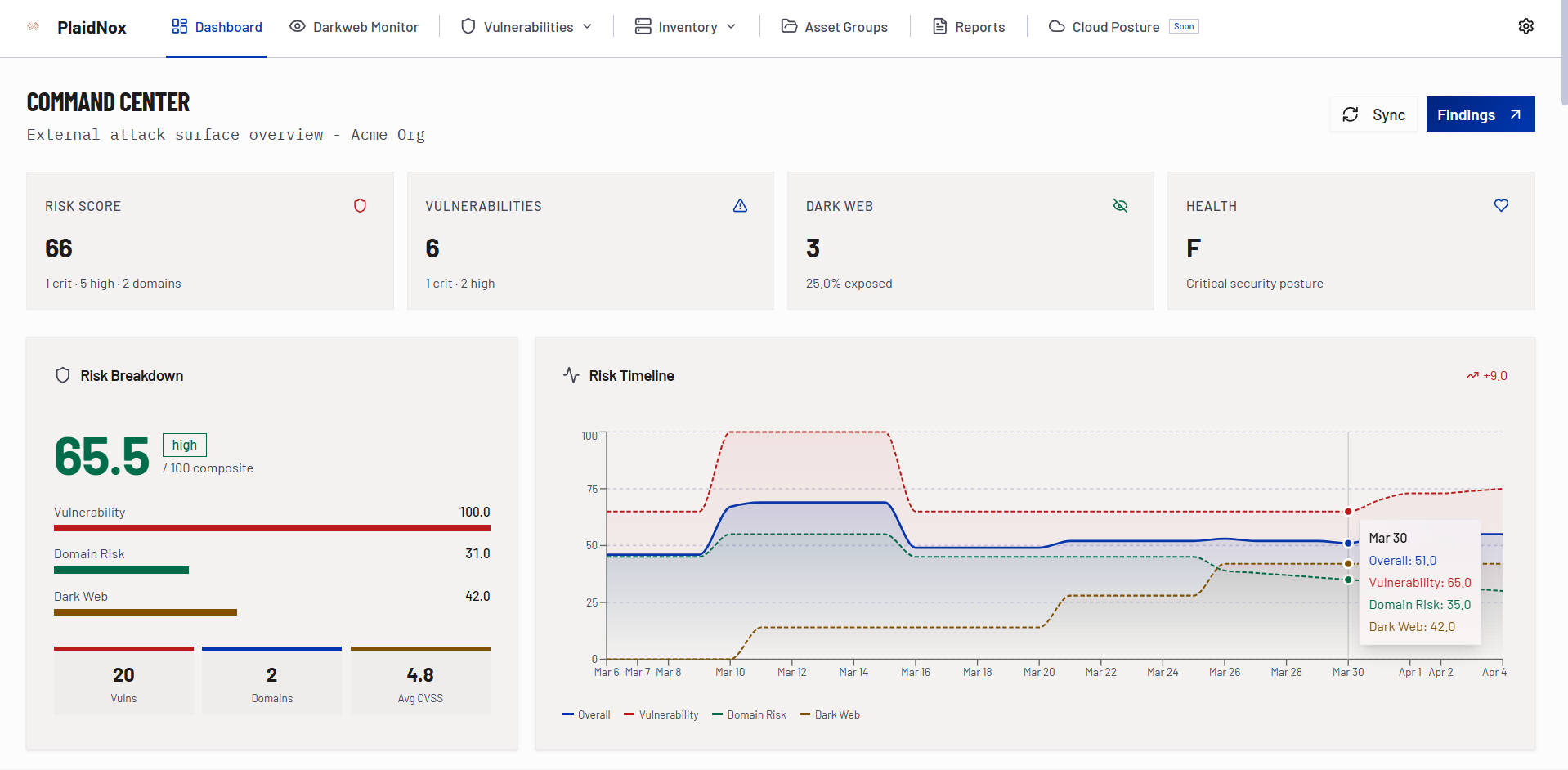
Veta Platform - Your Credential Intelligence Hub
Manage all credential monitoring, track exposure findings in real time, configure alerting rules, and download executive reports - all from one unified platform alongside ASM, CSPM, and Trinity AI.
- Real-time exposure dashboard
- Severity and trend analytics
- Remediation lifecycle tracking
- Multi-channel alert management
Intelligence That Drives Action
Every Veta Credential Monitor engagement delivers executive digests and enriched findings so leadership and security teams share the same view of credential exposure and remediation velocity.
- Executive summary with credential exposure risk assessment
- Enriched findings with blast-radius score and source attribution
- Employee vs. customer segmentation and affected service mapping
- Response playbook recommendations for each finding category
- Trend analysis showing exposure velocity and remediation progress
Why Security Teams Choose Veta Credential Monitor
- Blast-radius scoring prioritizes by real-world impact
- Human analyst validation - no raw, unverified dumps
- Real-time alerts, not weekly batch reports
- Employee vs. customer credential segmentation
- Part of Veta platform alongside ASM, CSPM, and Trinity AI
- Broad source coverage - stealer logs, forums, Telegram, paste sites
- Pre-built response playbooks for immediate remediation
- Continuous monitoring with < 4 hour alert time
Whether you are responding to a breach, preparing for compliance audits, or building proactive threat intelligence - Veta Credential Monitor delivers enriched dark web findings that help teams act, not just observe.
Know When Your Credentials Are Exposed
Stop waiting for breach notifications. Start with Veta Credential Monitor and get real-time dark web intelligence integrated into your security workflows.